A majority of news sites are susceptible to domain spoofing via techniques such as typosquatting. Typosquatting allows fake news peddlers to entrap readers who mistype news sites’ domains into their browsers.
And these typosquatters make it a point to copy the sites they spoof carefully from the domain name down to the logo and layout of their fake news pages. Possible motivations include extracting personally identifiable information (PII) from fake subscription forms, spreading malicious information, or dropping malware onto victims’ devices.
How Fake News Site Proliferate
Fake News Site Creation
Malicious actors first register a domain name that is as close as possible to that of the site they want to spoof. We have seen real news sites even report on how hackers attempted to pass off misinformation by banking on their reputation. An example would be Foreign Policy (FP)’s experience with pro-Iran hackers to cast Saudi Arabia and Tehran as aggressors just this May.


While there are stark differences in the banner and font, any reader who does not subscribe to FP would still be fooled by the fake news page. Anyone who doesn’t scrutinize domains can also easily fall for the ruse. The real FP site’s domain is foreignpolicy[.]com, while that of the spoofed site is foreignpolicy[.]net.
Content Theft
Once the website is ready, the fake news producers fill it with content. Some fake news sites create all of its own content, passing each one off as real news. But others who only want to spread one or a few fake articles, for instance, opt instead to steal the content, preferably of the site they are spoofing.
Social Media Promotion and Advertising
Like real news reporters, fake news writers need to make a living. So some fake news sites publish ads. Then again, they would need readers to click those ads and they may use social media to promote their publications.
Our Investigative Tool: WHOIS Search
We’ve seen the perils of believing in fake news such as instigating riots, causing fake memories, distorting truths, and more, but people still keep falling for them. Maybe people’s judgment skills can be supplemented by technology, especially in the workplace.
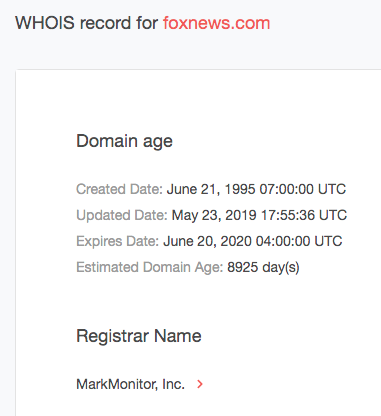
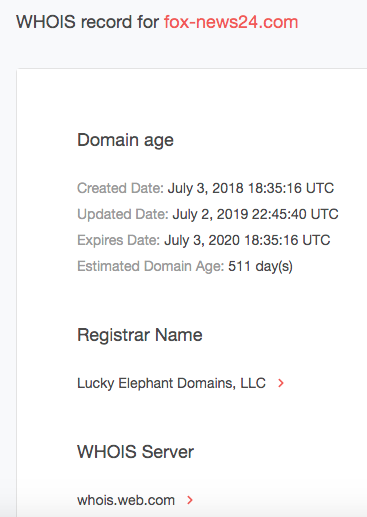
We obtained a list of confirmed fake news sites from GitHub and subjected some of these to WHOIS Search checks. We compared the WHOIS records of foxnews.com (the real deal) with a spoofed version of it, fox-news24[.]com.
The table below sums up the differences between both domains:
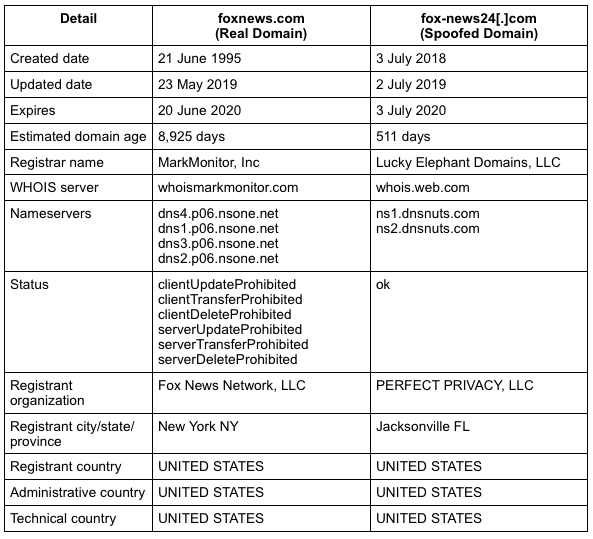
Clearly, fox-news24[.]com is not owned by Fox News Network, nor does it have any ties to the media giant. Why is that? First off, fox-news24[.]com has a recent registration date. Note that it’s common for cybercriminals to use newly-registered domains as part of their fraud.
Additionally, the information on the spoofed domain is redacted. It can be because site owners are hiding from law enforcement as more than half of existing fake news sites in this study have used a WHOIS privacy protection service to hide their personal details. However, a lot of websites use domain privacy services and are entirely legitimate, as in the case of The Republican-American (rep-am[.]com), a Pulitzer-prize winning site.
Still, it’s interesting to note that established media outfits like foxnews[.]com typically have age-old operational sites and tend to make their contact details public.
Based on this brief analysis, it may be a good idea to block the spoofed domain fox-news24[.]com from your corporate network so employees won’t land on a potentially harmful, not to mention dishonest, site.
WHOIS Search is a great tool to start investigating the veracity of suspicious domains since it can identify who is behind a website. By digging deeper into the WHOIS records of a domain name, users can make sure that they are not patronizing fake news sites. Integrating its restful API counterpart, WHOIS API, into security solutions, can also help companies prevent employees from landing on dubious sites automatically.
Other products can also bring a deeper perspective on a domain’s past as some news sites become crooked only after they change hands. Bearing this in mind, domain ownership history can be monitored with WHOIS History Search and WHOIS History API.





