Hundreds of thousands of domain names are registered every day. While this may be consistent with the trend of shifting almost everything online, a significant share of these registrations might be dubious at best. Reports revealed that 70% of newly registered domains were deemed “malicious” or “suspicious” in 2019.
But how can you tell if new domains are safe or not? One way is to monitor them with a newly registered domains database, particularly for three types of domain names.
Machine-Generated Domain Names
Developers of malware typically use machines to generate various domain names to spread their nefarious creations and enable these to communicate with their command-and-control (C&C) servers. While threat actors use different algorithms, the end goal is always to evade detection by security systems.
What appear to be machine-generated domain names, however, can be spotted within a newly registered domains database, as these contain a random series of alphanumeric characters. Among the new domain names under the .com top-level domain (TLD) that appeared in the Domain Name System (DNS) on 18 October 2020, for example, were thousands of domains that looked like a machine generated them. Some examples are:
- 00-00-03[.]com
- 0-000-04[.]com
- 000-123[.]com
- 000pet[.]com
- 001flyhosting[.]com
- 001jjt[.]com
- 005123com[.]com
- 007ent[.]com
- 0081love[.]com
- 00gew[.]com
Typosquatting Domain Names
Typosquatting occurs when a domain name that resembles that of a famous brand or company is registered in bad faith. These domain names could be used to lure unsuspecting victims into opening a phishing email. In such a case, victims could open their network to data-stealing malware. Most threat actors take advantage of popular and reputable brands to gain their victims’ trust.
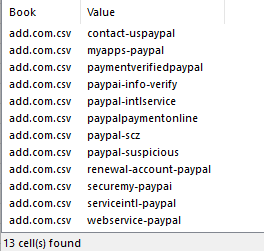
In the newly registered domains database downloaded on 18 October 2020, some domain names were similar to those of PayPal, Walmart, Bank of America, and Microsoft, among others. Below is a screenshot of the PayPal-lookalike domain names from the newly registered domains database.
Aside from phishing, typosquatting domain names can also be used in smear campaigns against a company.
Punycode Domain Names
The classic typosquatting domain names use misspelled variations of the imitated entity’s name. As such, threat actors register walmort[.], waiImart[.]com, and others in a bid to victimize Walmart customers. They could also use other TLDs such as .top, .biz, and .net.
A more undistinguishable form of typosquatting is when threat actors use Punycode. Punycode makes it possible for Unicode characters to be used in domain names so that people can easily remember domain names in the local context. But threat actors often abuse the functionality to make victims believe that they are visiting the imitated brand’s official website.
A few examples of Punycode domain names and how they appear in the newly registered domains database are listed below.
- ḭnstagram[.]com (xn--nstagram-s29c[.]com)
- ʍicrosoft[.]com (xn--icrosoft-93d[.]com)
- offĭce365[.]com (xn--offce365-ujb[.]com)
- appłeid[.]com (xn--appeid-5db[.]com ap)
- outlooĸ[.]com (xn--outloo-8bb[.]com)
Domain Names Inspired by Current Events
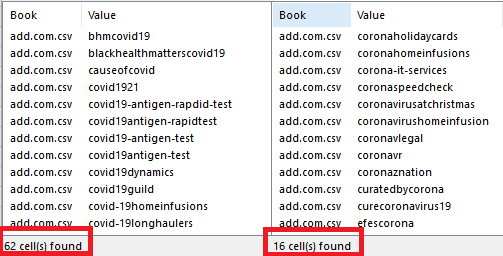
Threat actors are known to take advantage of newsworthy events, so if you have been monitoring the newly registered domains database, you would have noticed a sudden spike in COVID-19- and coronavirus-inspired domain names beginning in March.
Up until now, dozens of pandemic-themed newly registered domain names appear on the DNS. In the downloaded newly registered domains database, 62 domain names contained the string “covid,” while 16 contained “corona.”
The same trend was observed a few days after the death of George Floyd in May. Domain names containing his name and the string “blacklivesmatter” were bulk-registered daily.
Domain names inspired by current events, of course, may not all be malicious. However, individuals and enterprises must observe caution when dealing with them, as they could be used in phishing campaigns or financial scams.
Domain names are registered by the thousands every day, and what we presented here are just four types of domain names worth observing. Having a newly registered domains database makes it easy for companies to monitor suspicious domain names to warn employees and other network users to look out for and hopefully avoid them.





